Couple of days ago, the world's cyber crime media has announced the arrest of Cron. This "little" gang - stolen nearly 1 million from russian banks after infecting over one million Android smart phones with a mobile Trojan called "CronBot". 85% of the world population uses Android. This gang had big plans for France but got shut down just before.
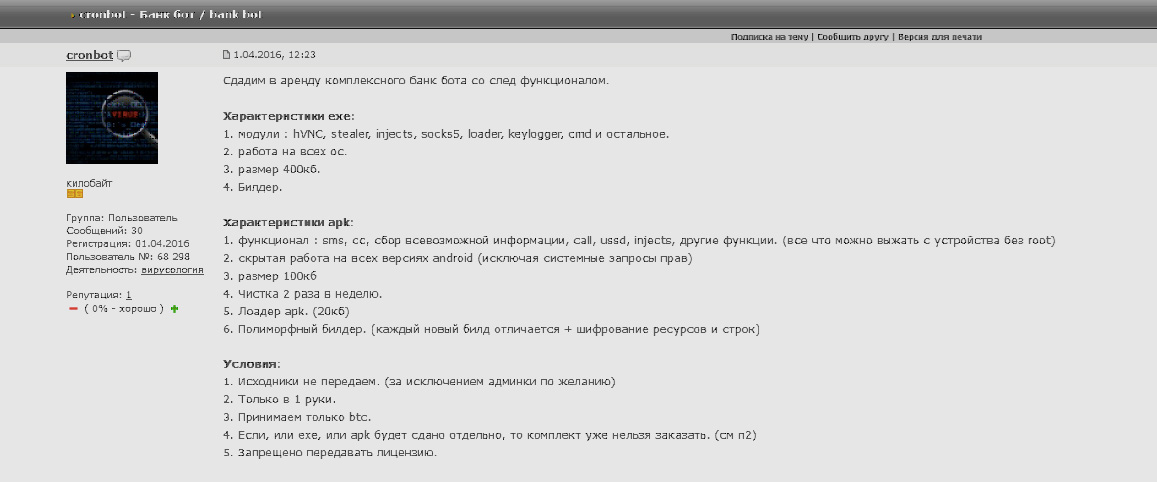
Every day Cron malware attempted to steal money from 50-60 clients of different banks. The gang's infection vector included spam SMS messages and fake applications.
The Cron malware gang abused the popularity of SMS-banking services and distributed the malware onto victims' Android devices by setting up apps designed to mimic banks' official apps.
They targeted customers of Sberbank, Alfa Bank, and online payments company Qiwi, exploiting SMS text message transfer services.
But a the "how" question still remain, how this major gang operating carefully got caught by the Russian authorities?
Cron planned to start their "international activity" with attacks targeting banks of France. They developed special web injections for the following French financial institutions: Credit Agricole, Assurance Banque, Banque Populaire, BNP Paribas, Boursorama, Caisse d'Epargne, Societe Generale and LCL.
However, by November 2016, Russian legal enforcement with support from Group-IB had managed to identify all members of the group and collect digital evidence of the crimes committed. On November 22, 2016, a large-scale operation was carried out in 6 Russian regions: 16 Cron members were detained. The last active member of the group was detained in early April in St. Petersburg.


Comments
Post a Comment