This past Thursday, a former University of Iowa student appeared in court on charges of hacking his school and professors and changing grades for himself and a few other fellow students.
The FBI arrested the suspect — Trevor Graves, age 22 — at the end of October, in Denver, his hometown. According to an FBI arrest warrant, the teenager planted hardware keyloggers on several school computers.
Student used hardware keylogger
Graves had help from other students. One would plant the keylogger, while the other would attend class and confirm a teacher had logged into his school account.They would then retrieve the keylogger and extract the login credentials. University of Iowa did not implement two-factor authentication for its student management system, so the login credentials allowed Graves access to teachers' accounts.
This took place for a period of 21 months, between March of 2015 to November of 2016.
The scheme unfolded when a teacher noticed in mid-December 2016 that some of Graves' grades had changed without her knowledge. The professor informed the University's IT staff, who investigated and found the keyloggers. The FBI was called in to aid the investigation.
Graves changed grades over 90 times in 21 months
All in all, they found that Graves changed grades more than 90 times, for him and five classmates. They also found that he regularly stole exams and shared tests with other students.On December 29, 2016, the FBI and University of Iowa Police executed a search warrant at Graves' home, an off-campus apartment in Iowa City.
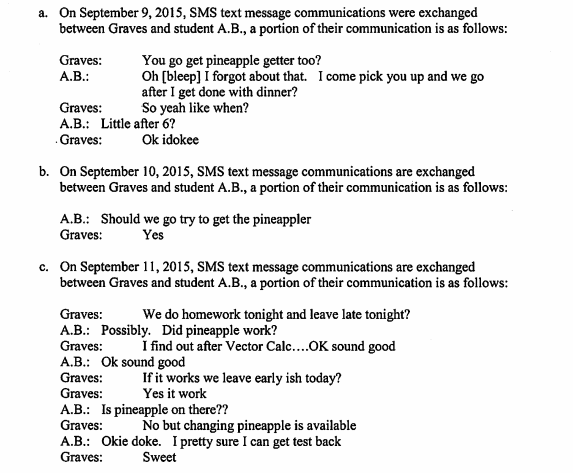
Investigators found keyloggers, phones, and thumb drives with compromising information. The phones contained records of past conversations between graves and his co-conspirators, while the thumb drives contained copies of stolen exams. Graves referred to the keyloggers using the term "pineapple."
Similar incident happened at Kansas University
In conversations with co-conspirators, Graves told them he could not change grades too significantly. Last spring, Kansas University expelled a student for a similar scheme. The unnamed student — not charged — used a similar hardware keylogger to steal teachers' login credentials and modify grades. That student changed F grades to A grades and was caught almost immediately, a reason why Graves' scheme lasted for 21 months.Because the damage of Graves' actions was over a $5,000 limit (investigation into the hack cost $67,500), authorities filed charges against Graves. If found guilty, he'll probably face probation and hours of community work, as most cases like these have concluded in the past.
Graves was also a member of the University's wrestling team.
Source: https://www.bleepingcomputer.com/news/security/student-arrested-for-using-keylogger-to-change-grades-over-90-times/


Comments
Post a Comment